SOC as a Service
Managed Security Services (MSS) refers to a service where organizations or enterprises outsource the monitoring of their cybersecurity devices (such as firewalls, Intrusion Detection Systems, Intrusion Prevention Systems, Web Application Firewalls, Active Directory, and antivirus software) or core system logs to professional cybersecurity vendors.
For clients with outsourced cybersecurity needs, ACSI offers safety and real-time security event monitoring and analysis services, 24 hours a day, 7 days a week, throughout the year.
ACSI utilizes Front-end Security Application (FSA) servers to host the logs of the devices or systems that clients wish to monitor externally. These logs are securely transmitted to our Security Operation Center (SOC) where we establish monitoring rules tailored to the applicable devices. In the event of abnormal behavior or suspected attack incidents, we proactively notify or contact the client immediately. Additionally, we regularly provide notification statistics and analysis results, along with the latest cybersecurity protection recommendations and insights, serving as crucial reference points for our clients' information security management.
In recent years, we established Intelligent Security Operations Center (Intelligent SOC) platform architecture. We conduct multidimensional correlation analysis across clients, devices, and extended periods, enabling effective detection and tracking of cybersecurity incidents. Coupled with real-time feedback to the monitoring center platform, our company's monitoring center can issue warning notifications to clients before hackers cause substantial damage to their environment. We provide comprehensive, effective, and high detection rate for cybersecurity event monitoring and analysis services. Combined with a professional operations and maintenance team with clearly defined roles, it forms the best SOC service team.
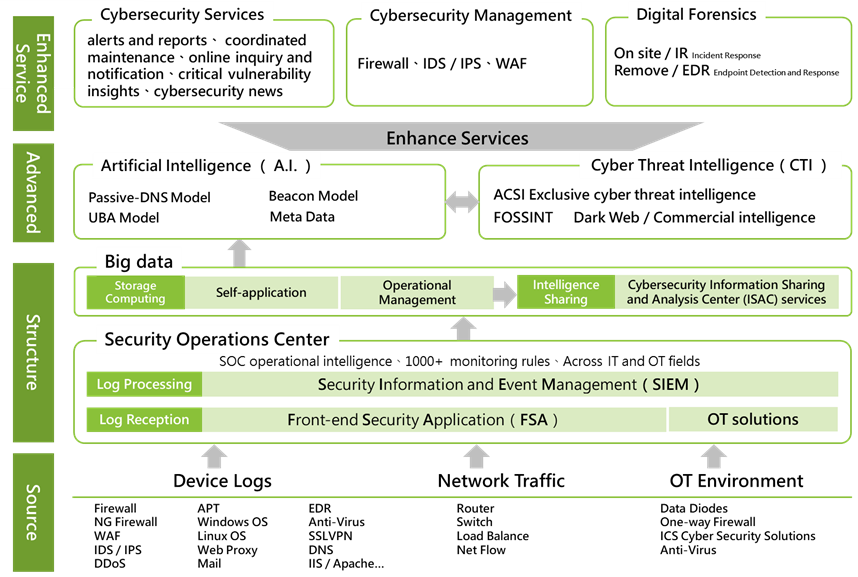
ACSI Intelligent SOC Platform Architecture
