【Service Features】
Unique ISO 17025 Lab certified and Security Operation Center (SOC) in-house developed domestic digital identification center (DIC), aimed at seamlessly integrating data security pre-incident monitoring (SOC service) and post-incident response and treatment (investigation and forensic service) to provide all round information security service.
Investigation and forensic service
【Service Introduction】
"Every step will show" and professional investigation and forensic will leave criminals no place to hide.
Advancing technology is changing acts of criminals at the same time. Scores of crimes are committed by new technology. To fight them you have to gather digital evidence. That is, you have to gather, secure, identify, analyze, and present digital evidence with advanced forensic technology to leave no place for criminals to hide.
ACSI has been acquiring a huge amount of investigation and forensic experience in the information security field based on its ever-increasing cases consulted by information security victims. As more and more customers are deeming investigation and forensic a critical professional service, ACSI is integrating its internal forensic resources into a digital forensic center (DFC) to provide customers with premium services.
As most cases may end up with related law suits, this service will conform to the requirements of "evidential validity by rigorous procedures and testimonial validity" and require a comprehensive investigation and forensic process. ACSI DFC not only implemented the ISO/IEC 17025 lab quality management system, but also got certified by Taiwan Accreditation Foundation (TAF) as an international ISO17025 test lab (code 3334). This enables identification results made by ACSI acceptable by every ISO standard compliant lab which ensures our customers get world class forensic service. ACSI is committed to setting up a robust and solid foundation of investigation and forensic services based on its professionalism in information security field and international standard certified service quality.
【Service Items】
-
Digital Evidence Secure
-
Digital Evidence Analysis
-
forensic Report Preparation
-
Hacker Invasion Investigation and forensic Service
-
Malware Investigation and Analysis Service
-
Data Leakage Investigation and forensic Service
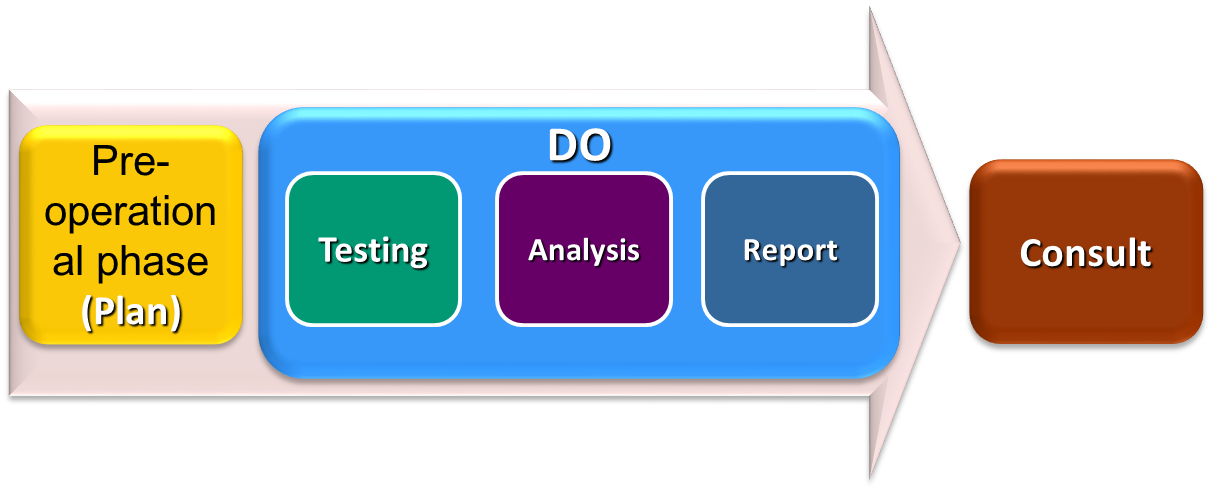
【Service Flow Chart】
Mobile APP for basic information security test service
【Service Introduction】
Thanks to the explosive development of mobile communication technology, the popularity of smart mobile devices and declining mobile networking expenses, emerging technologies including FinTech, mobile payment, industrial 4.0, IoT, and cloud application are breaking and remaking business models every day. Explosive growth of Mobile Applications (Apps) is affecting our daily life in almost every aspect. This, in spite of all the benefits that come with it, is giving malware and "traps" embedded in mobile Apps opportunities to threaten mobile service users.
Addressing concerns to mobile App security, the "Mobile App basic information security guidelines" and relevant test standards from the government are set to promote a test system, create a mobile App information security test system, and improve the information security quality of mobile App products.
Aimed at alignment with a government information security policy and providing customers with a complete interface security service, ACSI is striving to build up a mobile App information security test system. It is integrating mobile App basic information security testing into lab services according to a "mobile App basic information security self-diagnosis promotion system" by the Industrial Development Bureau, MOEA with the test standard based on the same mechanism. ACS DFC has been certified by TAF as an international ISO17025 test lab (code 3334) to provide customers with world class identification service.
【Service Items】
-
Mobile APP for information security test service
-
Mobile APP Basic information Security Test
-
Sensitive Data Protection Test
-
User ID, Permission, and Connection Management Security
-
Mobile App Source Code Security
-
Payment Control Security
【Service Flow Chart】